Last updated on Mar 26, 2026
Security Inspection Checklist free printable template
pdfFiller is not affiliated with any government organization
Why pdfFiller is the best tool for your documents and forms
End-to-end document management
From editing and signing to collaboration and tracking, pdfFiller has everything you need to get your documents done quickly and efficiently.
Accessible from anywhere
pdfFiller is fully cloud-based. This means you can edit, sign, and share documents from anywhere using your computer, smartphone, or tablet.
Secure and compliant
pdfFiller lets you securely manage documents following global laws like ESIGN, CCPA, and GDPR. It's also HIPAA and SOC 2 compliant.
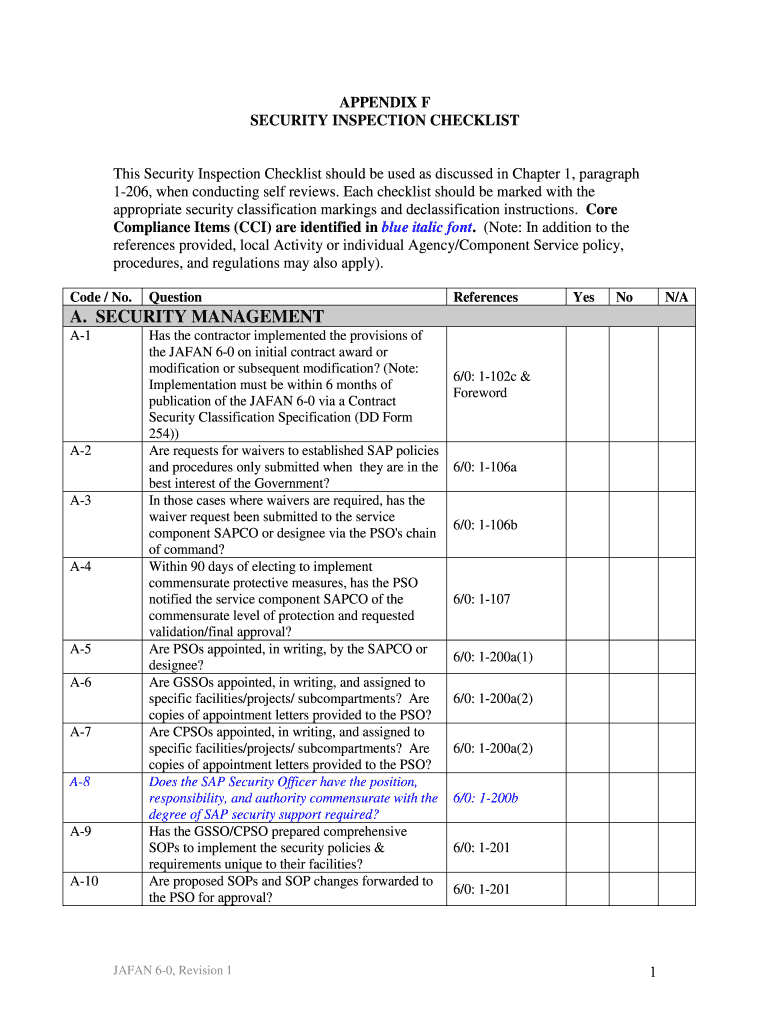
What is Security Inspection Checklist
The Security Inspection Checklist is a fillable document used by government entities to conduct self-reviews of security management and personnel security compliant with JAFAN 6-0 guidelines.
pdfFiller scores top ratings on review platforms




Who needs Security Inspection Checklist?
Explore how professionals across industries use pdfFiller.
Comprehensive Guide to Security Inspection Checklist
What is the Security Inspection Checklist?
The Security Inspection Checklist serves as a vital tool for ensuring security compliance within organizations. Its primary function is to facilitate security assessments in alignment with JAFAN 6-0 guidelines, which provide crucial frameworks for security management. This document is essential for evaluating compliance and identifying areas for improvement in security practices.
Additionally, the checklist features classification markings that ensure sensitive information is handled appropriately. Users must also follow declassification instructions, reflecting the document's role in maintaining confidentiality and security protocols.
Purpose and Benefits of the Security Inspection Checklist
The primary goal of utilizing the Security Inspection Checklist is to conduct thorough security assessments. Regular self-reviews with this checklist offer numerous benefits, including the identification of potential security gaps and the enhancement of existing security measures. By ensuring that organizations adhere to the required standards, the checklist promotes proactive security management.
By employing this security management checklist, organizations can maintain compliance with relevant regulations, ultimately safeguarding their operations and personnel.
Key Features of the Security Inspection Checklist
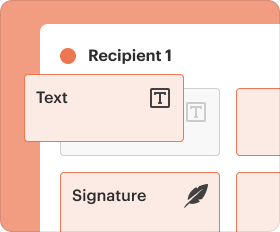
This checklist includes several key components designed to streamline the assessment process. Users will find fillable fields, checkboxes, and various question types to effectively capture relevant information. Each section focuses on critical aspects of security management and planning, making it easier for users to navigate their assessments.
-
Fillable fields for data entry
-
Checkboxes for quick responses
-
Specific guidelines for completing each section
Moreover, the inclusion of detailed instructions enhances clarity and encourages accurate completion of the form.
Who Needs the Security Inspection Checklist?
The Security Inspection Checklist is designed for various stakeholders, including contractors, security managers, and compliance officers. Each of these roles benefits from conducting security self-assessments to ensure adherence to government security requirements.
Organizations that have specific security obligations under governmental regulations should particularly prioritize the use of this checklist to uphold compliance and enhance security practices.
How to Fill Out the Security Inspection Checklist Online (Step-by-Step)
Completing the Security Inspection Checklist online involves a systematic approach. Users can follow these step-by-step instructions to ensure accurate submission:
-
Access the form through the provided online platform.
-
Complete all mandatory fields highlighted in the checklist.
-
For each question, select 'Yes', 'No', or 'N/A' per the guidelines.
-
Review your responses for accuracy before submission.
Additionally, focusing on specific fields and following instructions ensures a comprehensive assessment.
Review and Validation Checklist for the Security Inspection Checklist
Before submitting the completed checklist, it is crucial to ensure completeness and accuracy. Users should be vigilant for common errors, which can include incomplete answers or misinterpretation of questions.
Suggested final review steps include double-checking the filled-out sections and validating all information. This validation process is essential to prevent delays in compliance and ensure that all security protocols are accurately documented.
Submission Methods and Delivery of the Security Inspection Checklist
Once the checklist is completed, users have multiple submission methods available, including online and by mail. Clear instructions provided within the form guide users on confirming successful submission.
Additionally, understanding the processing times and potential rejection reasons can help manage expectations regarding compliance outcomes.
Importance of Security and Compliance for the Security Inspection Checklist
Adhering to security compliance is critical for organizations utilizing the Security Inspection Checklist. Following JAFAN 6-0 guidelines not only enhances security measures but also ensures data protection is prioritized.
Organizations must recognize the value of secure platforms, like pdfFiller, when handling sensitive documentation to maintain compliance and protect data.
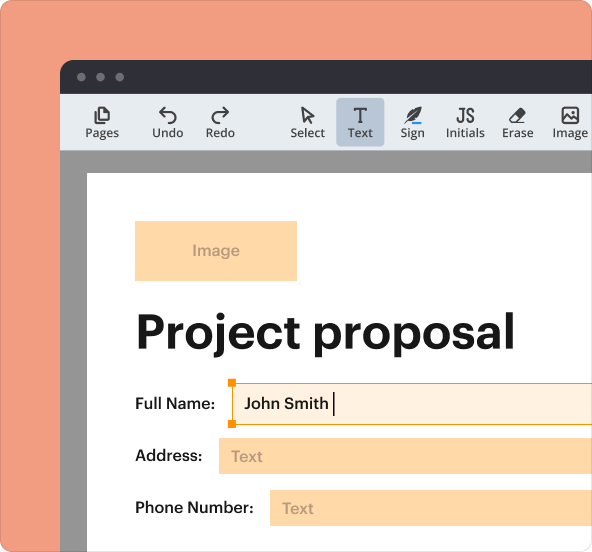
How pdfFiller Can Help with the Security Inspection Checklist
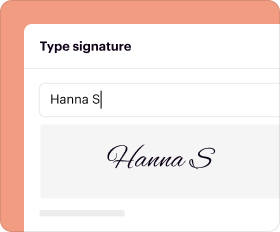
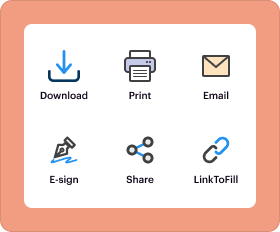
pdfFiller offers essential features that enhance the user experience when managing the Security Inspection Checklist. Users can edit, eSign, and track submissions seamlessly within the platform.
The robust security measures implemented by pdfFiller, including 256-bit encryption and compliance with HIPAA and GDPR regulations, ensure the protection of sensitive user data while completing and managing the checklist.
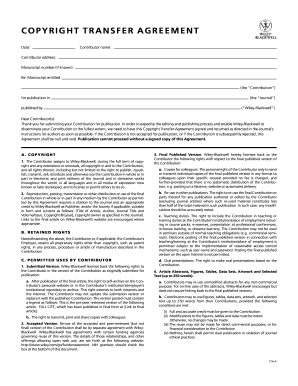
Sample of a Completed Security Inspection Checklist
Providing a visual reference, a sample of a completed Security Inspection Checklist can guide users in filling out their forms correctly. This sample illustrates how each section should be answered and emphasizes the importance of thorough completion.
Referencing this sample can significantly aid users in understanding how to effectively complete their own checklists.
How to fill out the Security Inspection Checklist
-
1.Access the Security Inspection Checklist on pdfFiller by searching its name in the search bar or browsing the Government Forms category.
-
2.Once opened, navigate through the document using the standard pdfFiller interface. Check for fillable fields indicated by blue outlines.
-
3.Before you start filling the form, gather necessary information such as security policies, previous inspection reports, and relevant guidelines to ensure accurate responses.
-
4.Begin completing the checklist by answering the posed questions. Utilize the multiple checkboxes to indicate 'Yes', 'No', or 'N/A' as applicable.
-
5.Fill in any required text fields with specific information relevant to your organization’s security practices.
-
6.Continue through the checklist, closely referencing the JAFAN 6-0 guidelines as you respond to ensure compliance.
-
7.Once all sections are completed, review your answers carefully. Ensure all fields are filled appropriately and that your responses are accurate.
-
8.Finalize the form by checking for any missed fields or responses, then click the save button. You can choose to download the completed form or submit it directly through pdfFiller.
-
9.To save the document, select the download option which allows you to choose your preferred file format. If submitting directly to an authority, follow any additional instructions they provide.
Who is eligible to use the Security Inspection Checklist?
The Security Inspection Checklist is designed for use by government officials, security personnel, contractors, and any entity involved in managing or assessing security compliance under JAFAN 6-0 guidelines.
Are there any deadlines for completing the Security Inspection Checklist?
While specific deadlines may vary based on agency requirements, it is advisable to complete the checklist during designated review periods or prior to scheduled compliance audits to ensure timely assessments.
What are the submission methods for the completed checklist?
Completed Security Inspection Checklists can typically be submitted electronically through designated platforms or printed and mailed to the relevant oversight authority, depending on their submission guidelines.
What supporting documents are needed when submitting the checklist?
Often, supporting documents may include previous inspection reports, security policies, and any compliance documentation relevant to the security management practices being reviewed.
What are common mistakes to avoid when filling out the checklist?
Common mistakes include leaving fields blank, misunderstanding questions, or failing to reference the latest JAFAN 6-0 guidelines, which can impact compliance assessment accuracy.
What is the processing time for submitted checklists?
Processing times can vary based on the agency handling the submission. Typically, you can expect a review period of several weeks, though urgent requests may be expedited based on need.
Are there any fees associated with submitting the Security Inspection Checklist?
Generally, there are no direct fees for submitting the checklist; however, other compliance-related services may incur fees based on the agency's policies.
Related Catalogs
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.